What is TeslaCrypt and AlphaCrypt?
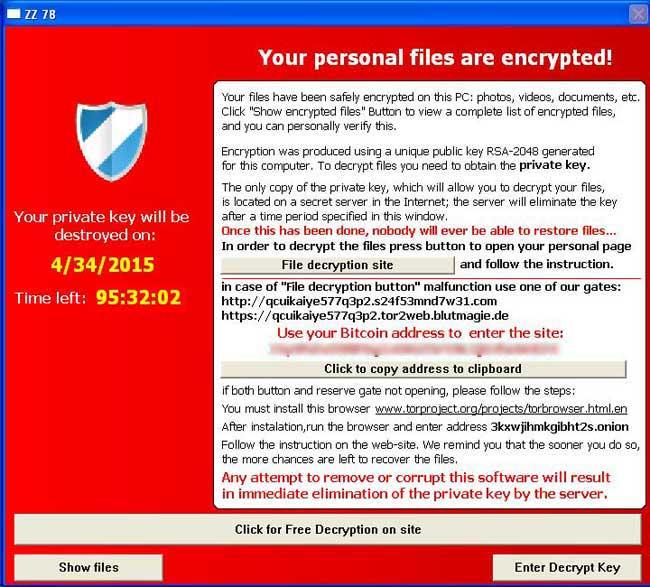
TeslaCrypt and Alpha Crypt are file-encrypting ransomware programs that target all version of Windows including Windows XP, Windows Vista, Windows 7, and Windows 8. TeslaCrypt was first released around the end of February 2015 and Alpha Crypt was released at the end of April 2015. When you are first infected with TeslaCrypt or Alpha Crypt they will scan your computer for data files and encrypt them using AES encryption so they are no longer able to be opened. Once the infection has encrypted the data files on all of your computer drive letters it will display an application that contains instructions on how to get your files back. These instructions include a link to a Decryption Service site, which will inform you of the current ransom amount, the amount of files encrypted, and instructions on how to make your payment. The ransom cost starts at around $500 USD and is payable via bitcoins. The bitcoin address that you submit payment to will be different for every victim.When TeslaCrypt or Alpha Crypt are first installed on your computer they will create a random named executable in the %AppData% folder. This executable will be launched and begin to scan all the drive letters on your computer for data files to encrypt. If a a supported data file is detected it will encrypt it and then append a new extension to the filename based on the particular variant you are infected with. For TeslaCrypt, the extension .ECC and .EXX will be appended and for Alpha Crypt the extension .EZZ will be appended to filenames.The main noticeable difference between TeslaCrypt and Alpha Crypt is that TeslaCrypt adds the .ECC and .EXX extensions to encrypted files and Alpha Crypt adds the .EZZ extension.The extensions targeted by TeslaCrypt are:.7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .sc2save, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mcgame, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .001, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .DayZProfile, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, .unity3d, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbfv, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odtThe extensions targeted by Alpha Crypt and newer versions of this family are:.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odtIt important to stress that both TeslaCrypt and Alpha Crypt will scan all drive letters on your computer including removable drives, network shares, and even DropBox mappings. In summary, if there is a drive letter on your computer it will be scanned for data files to encrypt by the ransomwareWhen the infection has finished scanning your computer it will also delete all of the Shadow Volume Copies that are on the affected computer. It does this so that you cannot use the shadow volume copies to restore your encrypted files. There are posts that state TeslaCrypt did not delete Shadow Volume Copies, but this is untrue. The command that is run to clear the Shadow Volumes is:vssadmin delete shadows /allNow that your computer's data has been encrypted it will display the TeslaCrypt or Alpha Crypt application. For both of the ransomware variants the screens are identical other than the application title. The application title denotes the version of the ransomware.
Alpha Crypt Screen
While encrypting your files, this ransomware also create a text file ransom note in each folder that a file has been encrypted and on the Windows desktop. The ransomware will also change your Windows desktop wallpaper to a BMP file located on the Windows desktop. For TeslaCrypt the text ransom note is called HELP_TO_DECRYPT_YOUR_FILES.txt or HELP_RESTORE_FILES.txt and the BMP file is called HELP_TO_DECRYPT_YOUR_FILES.bmp or HELP_RESTORE_FILES.bmp. For Alpha Crypt the files are called HELP_TO_SAVE_FILES.txt and HELP_TO_SAVE_FILES.bmp.Both the wallpaper and the text ransom note will contain the same information on how to access the payment site and get your files back. An example of the wallpaper can be seen below.
TeslaCrypt Wallpaper
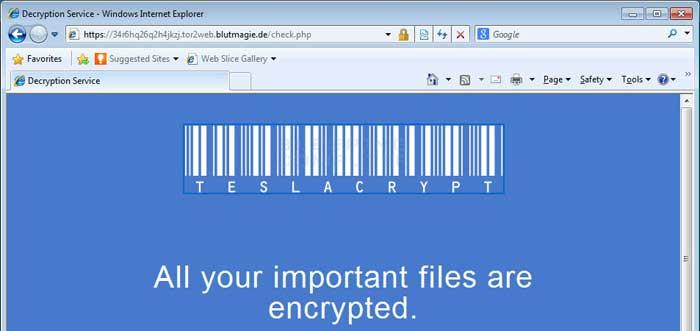
When you go to the URLs listed in the ransom note you will be taken to a TOR site where you can learn how much your ransom is and how to make the payment. The payment site for TeslaCrypt is called the TeslaCrypt Decryption Service and for Alpha Crypt it is called the Alpha Tool Decryption Service. TeslaCrypt differs from most other ransomware as being the first to accept PayPal My Cash cards. With the release of AlphaCrypt, PayPal My Cash Cards were removed as a payment option. For more details about the Decryption Service, please skip to this section.The text of the ransom application is:All your important files are encrypted!
Your personal files(including those on the network disks, USB, etc) have been encrypted: photos, videos, documents, etc. Click "Show files" Button to view a complete list of encrypted files, and you can personally verify this.Encryption was made using a unique strongest RSA-2048 public key generated for this computer. To decrypt files you need to acquire the private key.
The only copy of the private key, which will allow you to decrypt your files,is located on a secret TOR
server in the Internet; the server will eliminate the key after a time period specified in this window.
Once this has been done, nobody will ever be able to restore files...In order to decrypt files press button to open your personal page and follow the instruction. In case of "File decryption button" malfunction use one of public gates:
http://iq3ahijcfeont3xx.anfeua74x36.com or
https://iq3ahijcfeont3xx.tor2web.blutmagie.deUse your Bitcoin address to enter the site: <bitcoin address>if both button and reserve gates not opening, please follow these steps:
You must install TOR browser www.torproject.org/projects/torbrowser.html.en
After installation,run the browser and enter address iq3ahijcfeont3xx.onion
Follow the instructions on the web-site. We remind you that the sooner you do so,
the more chances are left to recover the files.There is no other way to restore your files except of making the payment.What should you do when you discover your computer is infected with TeslaCrypt or Alpha Crypt
Any attempt to remove or corrupt this software will result in immediate
elimination of the private key by the server.
If you discover that your computer is infected with TeslaCrypt you should immediately shutdown your computer and if possible create a copy, or image, of your hard drive. This allows you to save the complete state of your hard drive in the event that a free decryption method is developed in the future. For more information on how to do this, feel free to ask in the forums.If you do not plan on paying the ransom and can restore from a backup, then scan your computer with an anti-virus or anti-malware program and let it remove everything. Unfortunately, most people do not realize TeslaCrypt or Alpha Crypt is on their computer until it displays the ransom note and your files have already been encrypted. The scans, though, will at least detect and remove any other malware that may have been installed along with the ransomware program.As always we never recommend you pay the ransom, but if you do plan on doing so it is important that you do not delete anything from your computer. This is because the payment site may need certain files created by the infection to properly deliver you your key.Some of the folders and file locations where associated malware have been found are:%Temp%
C:\<random>\<random>.exe
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
How do you become infected with TeslaCrypt or Alpha Crypt?
A user is typically infected by TeslaCrypt or Alpha Crypt when they visit a hacked web site running an exploit kit and have outdated programs on their computer. In order to distribute their malware, developers will hack web sites and install a special software called an exploit kit that attempts to exploit vulnerabilities found in programs on your computer. The programs that are typically exploited include Java, Adobe Flash, Acrobat Reader, and Windows vulnerabilities. When an exploit kit successfully exploits your computer, it will install and start the ransomware without your knowledge.Therefore, it is imperative that everyone keeps Windows and their installed programs up-to-date. You can use these tutorials for more information on keeping your Windows installation and installed programs updated:TeslaCrypt and it's targeting of Games
TeslaCrypt was the first ransomware to actively target data files used by PC video games. The game files being targeted belonged to games such as RPG Maker, Call of Duty, Dragon Age, StarCraft, MineCraft, World of Warcraft, Diablo, Fallout 3, Half Life 2, Skyrim, Day Z, League of Legends, World of Tanks, Steam, and many more. Though it is unknown if targetting games increased revenue for the malware developers, Alpha Crypt continues to target the same data files.Though this was newsworthy, it is important to remember that TeslaCrypt and Alpha Crypt also happily encrypt your documents and images as well.What you need to know about TeslaCrypt, Alpha Crypt, and Network Shares
TeslaCrypt and Alpha Crypt will encrypt data files on network shares only if that network share is mapped as a drive letter on the infected computer. If it is not mapped as a drive letter, then TeslaCrypt will not encrypt any files on a network share.It is still strongly suggested that you secure all open shares by only allowing writable access to the necessary user groups or authenticated users. This is an important security principle that should be used at all times regardless of infections like these.Decryption Service Site (TeslaCrypt and Alpha Crypt Payment Site)
The developers of TeslaCrypt created a TOR web site that victims can use to pay the ransom and decrypt their files. This web site is titled the Decryption Service, for TeslaCrypt, and the Alpha Tool Decryption Service, for Alpha Crypt. When you visit this site you will get information information about your encrypted files, learn how to pay the ransom, be given the ability to decrypt one file for free, and support page where you can receive "help" from the malware developers. Links to this site can be found in the HELP_TO_SAVE_FILES.txt and the HELP_TO_DECRYPT_YOUR_FILES.txt ransom notes that are found on your Windows desktop. Once you visit the site you can pay the ransom, which is currently between $300-$500 USD by sending Bitcoins to a specified address.
Once a payment is made it must have a certain amount of bitcoin confirmations before your private key will be made available to you. Once these confirmations have occurred, this information will appear on the payment site and you can input it into the ransomware application on your computer to decrypt your files.Will paying the ransom actually decrypt your files?
First and foremost, only pay the ransom if you have absolutely no choice. By paying the ransom you just encourage the malware developers to continue making ransomware like TeslaCrypt and Alpha Crypt. If you have no choice, then paying the ransom will allow you to retrieve the keys necessary to decrypt your files. Once you pay the ransom and it is verified, information will be provided to you that you enter into the main application. You can then use it to decrypt your files. Please note that the decryption process can take quite a bit of time.Is it possible to decrypt .ECC, EZZ, and .EXX files encrypted by TeslaCrypt and Alpha Crypt?
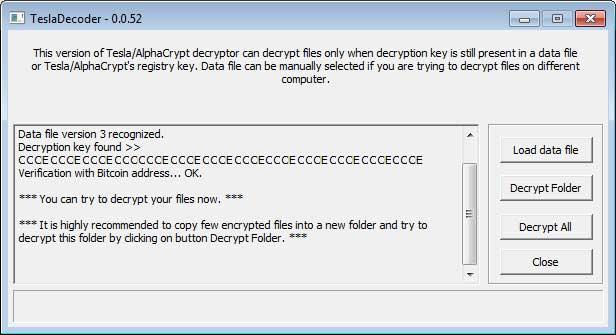
The good news is that if you are infected with TeslaCrypt (.ECC and .EXX file extensions) or Alpha Crypt (.EZZ extension) then it may be possible to decrypt your files for free using either TeslaDecoder or Cisco's TeslaDecrypt. At the time of this writing, TeslaDecoder is able to decrypt .ECC, .EZZ, and .EXX files encrypted by all versions of TeslaCrypt and Alpha Crypt. Unfortunately, TeslaDecrypt is only currently able to decrypt the original .ECC TeslaCrypt files. At this time we suggest you first use TeslaDecoder when trying to decrypt your files as it is being actively updated.It should be noted that there is no guarantee that either program will be able to restore your files. In these situations, the only methods you have of restoring your files is from a backup, file recovery tools, or if your lucky from Shadow Volume Copies. More information on how to possibly restore your files can be found in the next section.
Information on TeslaDecoder:On May 13th, 2015 one of our members named BloodDolly released his own TeslaCrypt and Alpha Crypt decrypter called TeslaDecoder. TeslaDecoder is able to decrypt .ECC, .EXX, and .EZZ files encrypted by both TeslaCrypt and Alpha Crypt and is currently the recommended utility to decrypt your files.TeslaDecoder can be downloaded from the following URL: http://www.dropbox.com/s/abcziurxly2...coder.zip?dl=0Once downloaded, extract the zip file and launch TeslaDecoder.exe. When started, TeslaDecoder will search for your storage.bin or key.dat files and attempt to retrieve the key from it. If it is successful, you will be shown an image similar to the one below. If TeslaDecoder states that it is unable to find your data file, you can load the storage.bin or key.dat file manually by clicking on the Load data file button.
TeslaDecoderIt is suggested that you test the decryption by copying a few encrypted files into a new folder and selecting the Decrypt Folder button. This will allow you to test the decryption key only on the files in the selected folder. If TeslaDecoder is able to properly decrypt your files, you can then use the Decrypt All button to decrypt all encrypted files on your computer.
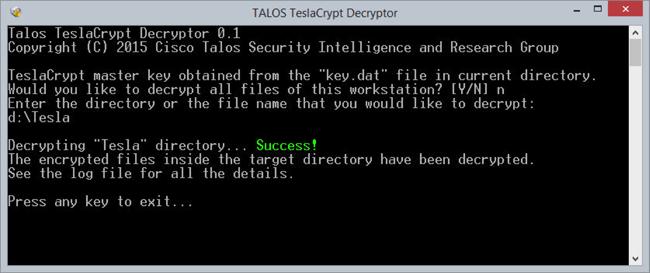
Information on Cisco's TeslaDecrypt:On April 27, 2015 the Cisco Talos Group posted an analysis of the TeslaCrypt ransomware along with a tool that may allow you to decrypt your files for free. The tool relies on certain information being stored in the %AppData%\key.dat file. If the tool is able to extract your key from the key.dat file, it will prompt you to decrypt your data. Unfortunately, the decryption key is sometimes stripped from this file making decryption not possible. The developer hopes to be able to use other methods in the future to retrieve the decryption key. Unfortunately, this method does not work for files encrypted with a .EXX extension.To see if the tool can decrypt your TeslaCrypt encrypted files you will need to download Cisco's TeslaDecrypt tool from the following link:Once the file is downloaded, unzip it and run it. TeslaDecrypt will search your hard drive for the key.dat file and try to recover the master key. If it is able to do so, it will prompt if you wish to decrypt the whole computer or a specific folder.
How to restore files encrypted by TeslaCrypt and Alpha Crypt
If TeslaDecrypt cannot find a key.dat file, search your hard drive for the file and move it to the same folder as TeslaDecrypt and try again. The key.dat file is usually located in the %AppData% folder.
For support on using TeslaDecrypt, please visit this topic:
If your files have become encrypted and you are not going to pay the ransom then there are a few methods you can try to restore your files.Method 1: BackupsThe first and best method is to restore your data from a recent backup. If you have been performing backups, then you should use your backups to restore your data.Method 2: File Recovery SoftwareWhen TeslaCrypt and Alpha Crypt encrypt a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you can use file recovery software such as R-Studio or Photorec to possibly recover some of your original files. It is important to note that the more you use your computer after the files are encrypted the more difficult it will be for file recovery programs to recover the deleted un-encrypted files.Method 3: Shadow Volume CopiesAs a last resort, you can try to restore your files via Shadow Volume Copies. Unfortunately, this infection will attempt to delete any Shadow Volume Copies on your computer, but sometimes it fails to do so and you can use them to restore your files. For more information on how to restore your files via Shadow Volume Copies, please see the link below:Method 4: Restore DropBox FoldersIf you had your dropbox account mapped as a drive letter then it is possible that its contents were encrypted by TeslaCrypt or Alpha Crypt. If this is the case you can use the link below to learn how to restore your files.How to restore files encrypted by TeslaCrypt and Alpha Crypt using Shadow Volume Copies
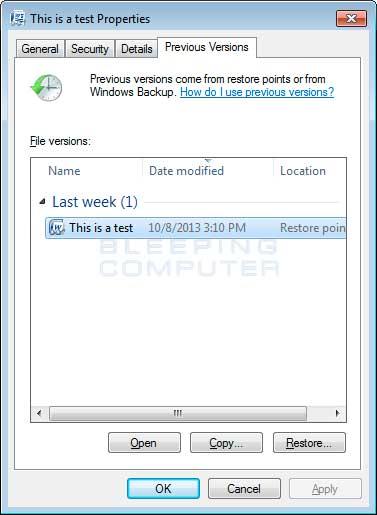
If you had System Restore enabled on the computer, Windows creates shadow copy snapshots that contain copies of your files from that point of time when the system restore snapshot was created. These snapshots may allow us to restore a previous version of our files from before they had been encrypted. This method is not fool proof, though, as even though these files may not be encrypted they also may not be the latest version of the file. Please note that Shadow Volume Copies are only available with Windows XP Service Pack 2, Windows Vista, Windows 7, & Windows 8.Note: TeslaCrypt and Alpha Crypt will attempt to delete all shadow copies when you first start any executable on your computer after becoming infected. Thankfully, the infection is not always able to remove the shadow copies, so you should continue to try restoring your files using this method.In this section we provide two methods that you can use to restore files and folders from the Shadow Volume Copy. The first method is to use native Windows features and the second method is to use a program called Shadow Explorer. It does not hurt to try both and see which methods work better for you.Using native Windows Previous Versions:To restore individual files you can right-click on the file, go into Properties, and select the Previous Versions tab. This tab will list all copies of the file that have been stored in a Shadow Volume Copy and the date they were backed up as shown in the image below.To restore a particular version of the file, simply click on the Copy button and then select the directory you wish to restore the file to. If you wish to restore the selected file and replace the existing one, click on the Restore button. If you wish to view the contents of the actual file, you can click on the Open button to see the contents of the file before you restore it.This same method can be used to restore an entire folder. Simply right-click on the folder and select Properties and then the Previous Versions tabs. You will then be presented with a similar screen as above where you can either Copy the selected backup of the folder to a new location or Restore it over the existing folder.
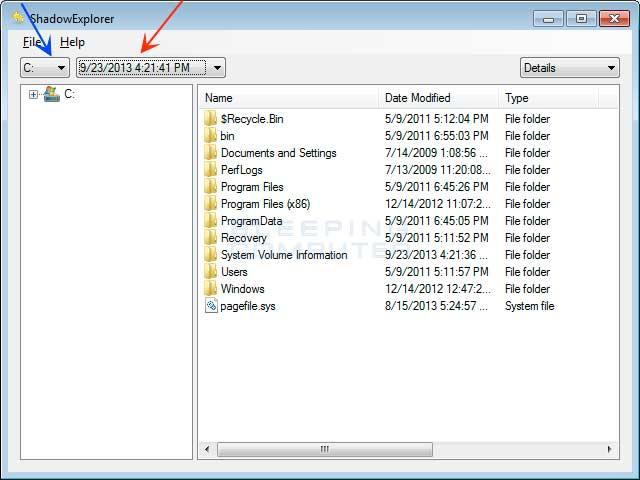
Using Shadow Explorer:You can also use a program called Shadow Explorer to restore entire folders at once. When downloading the program, you can either use the full install download or the portable version as both perform the same functionality.When you start the program you will be shown a screen listing all the drives and the dates that a shadow copy was created. Select the drive (blue arrow) and date (red arrow) that you wish to restore from. This is shown in the image below.To restore a whole folder, right-click on a folder name and select Export. You will then be prompted as to where you would like to restore the contents of the folder to.How to restore files that have been encrypted on DropBox folders
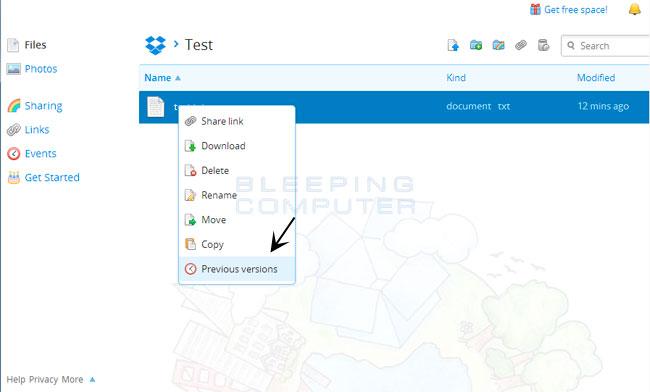
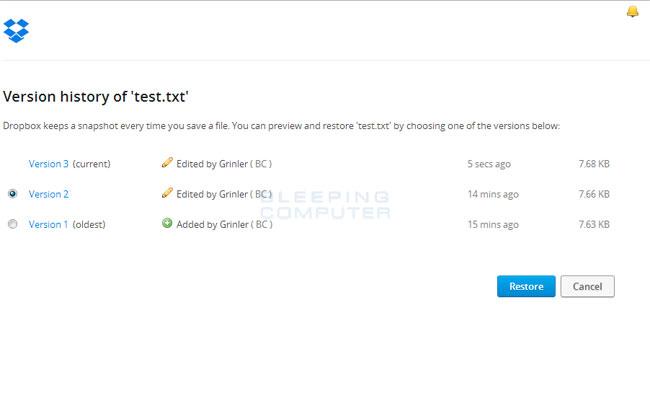
If you have DropBox mapped to a drive letter on an infected computer or synchronized to a folder, TeslaCrypt and Alpha Crypt will attempt to encrypt the files on it. DropBox offers free versioning on all of its accounts that will allow you to restore encrypted files through their website. Unfortunately, the restoral process offered by DropBox only allows you to restore one file at a time rather than a whole folder. If you need instructions on restoring an entire folder in DropBox, please click here.To restore a file, simply login to the DropBox web site and navigate to the folder that contains the encrypted files you wish to restore. Once you are in the folder, right-click on the encrypted file and select Previous Versions as shown in the image below.When you click on Previous versions you will be presented with a screen that shows all versions of the encrypted file.Select the version of the file you wish to restore and click on the Restore button to restore that file.Unfortunately the process outlined above can be very time consuming if there are many folder to restore. In order to restore an entire folder of encrypted files, you can use the dropbox-restore python script located here. Please note that this script requires Python to be installed on the encrypted computer to execute the script. Instructions on how to use this script can be found in the README.md file for this project.How to prevent your computer from becoming infected by TeslaCrypt and Alpha Crypt
There are a few methods and utilities that we recommend in order to protect your computer from ransomware infections. Two of the methods are the CryptoMonitor and HitmanPro: Alert programs and the third is to utilize Software Restriction Policies so that programs cannot run from certain locations. In full disclosure, BleepingComputer.com makes a commission off of the sales of CryptoPrevent and HitmanPro: Alert, but does not from CryptoMonitor.CryptoMonitor:
CryptoMonitor is a highly recommended program that is designed to detect when a ransomware is trying to encrypt your data and block it before it is able to do so. We have personally tested this application against CryptoWall, TeslaCrypt, Alpha Crypt, CryptoWall, and other smaller ransomware infections and CryptoMonitor was able to stop the infections before they could damage our data. The nice thing about CryptoMonitor is that it has a small footprint, does not use a lot of computer resources, is inexpensive, and is designed for one thing; to kill ransomware before they can encrypt your data. Please note that for the program to be fully effective, you should purchase the Pro version as it can block injected ransomware processes.You can find more information about CryptoMonitor at this link: https://www.easysyncsolutions.com/cr...ordetails.htmlHitmanPro: Alert:
HitmanPro: Alert is a great program as well but is designed as a full featured anti-exploit program and is not targeted exclusively at ransomware infections. Alert provides protection from computer vulnerabilities and malware that attempts to steal your data. Unfortunately, because this program has a much broader focus it sometimes needs to be updated as new ransomware is released. As long as you stay on top of the updates, HitmanPro: Alert offers excellent protection.You can find more information about HitmanPro: Alert here: http://www.surfright.nl/en/alertSoftware Restriction Policies:
You can use the Windows Group or Local Policy Editor to create Software Restriction Policies that block executables from running when they are located in specific paths. For more information on how to configure Software Restriction Policies, please see these articles from MS:The file paths that have been used by this infection and its droppers are:C:\Users\<User>\AppData\Local\<random>.exe (Vista/7/8)
C:\Users\<User>\AppData\Local\<random>.exe (Vista/7/8)
C:\Documents and Settings\<User>\Application Data\<random>.exe (XP)
C:\Documents and Settings\<User>\Local Application Data\<random>.exe (XP)
%Temp%
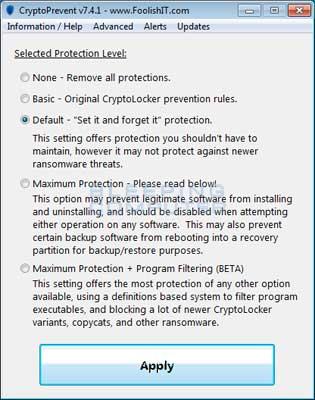
C:\WindowsIn order to block the TeslaCrypt you want to create Path Rules so that they are not allowed to execute. To create these Software Restriction Policies, you can either use the CryptoPrevent tool or add the policies manually using the Local Security Policy Editor or the Group Policy Editor. Both methods are described below.Note: If you are using Windows Home or Windows Home Premium, the Local Security Policy Editor will not be available to you. Instead we suggest you use the CryptoPrevent tool, which will automatically set these policies for you.How to use the CryptoPrevent Tool:
FoolishIT LLC was kind enough to create a free utility called CryptoPrevent that automatically adds the suggested Software Restriction Policy Path Rules listed above to your computer. This makes it very easy for anyone using Windows XP SP 2 and above to quickly add the Software Restriction Policies to your computer in order to prevent TeslaCrypt and Zbot from being executed in the first place. This tool is also able to set these policies in all versions of Windows, including the Home versions.
A new feature of CryptoPrevent is the option to whitelist any existing programs in %AppData% or %LocalAppData%. This is a useful feature as it will make sure the restrictions that are put in place do not affect legitimate applications that are already installed on your computer. To use this feature make sure you check the option labeled Whitelist EXEs already located in %appdata% / %localappdata% before you press the Block button.You can download CryptoPrevent from the following page:For more information on how to use the tool, please see this page:Tip: You can use CryptoPrevent for free, but if you wish to purchase the premium version you can use the coupon code bleeping30off to get 30% off. The premium version includes automatic and silent updating of application and definitions on a regular schedule, email alerts when an application blocked, and custom allow and block policies to fine-tune your protection.Once you run the program, simply click on the Apply Protection button to add the default Software Restriction Policies to your computer. If you wish to customize the settings, then please review the checkboxes and change them as necessary. If CryptoPrevent causes issues running legitimate applications, then please see this section on how to enable specific applications. You can also remove the Software Restriction Policies that were added by clicking on the Undo button.How to manually create Software Restriction Policies to block TeslaCrypt:
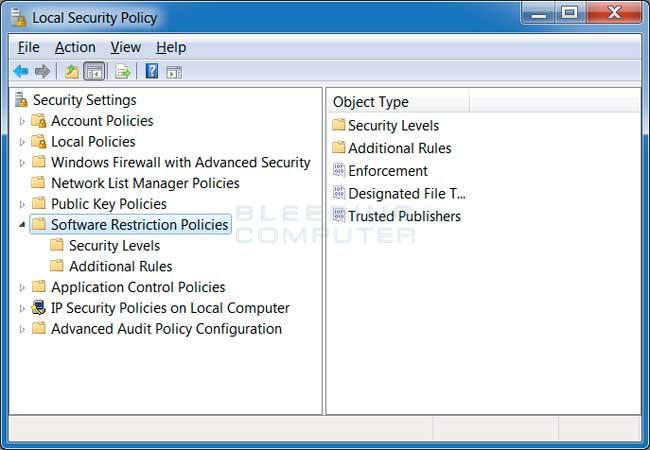
In order to manually create the Software Restriction Policies you need to be using Windows Professional or Windows Server. If you want to set these policies for a particular computer you can use the Local Security Policy Editor. If you wish to set these policies for the entire domain, then you need to use the Group Policy Editor. Unfortunately, if you are a Windows Home user, the Local Policy Editor is not available and you should use the CryptoPrevent tool instead to set these policies. To open the Local Security Policy editor, click on the Start button and type Local Security Policy and select the search result that appears. You can open the Group Policy Editor by typing Group Policy instead. In this guide we will use the Local Security Policy Editor in our examples.Once you open the Local Security Policy Editor, you will see a screen similar to the one below.Once the above screen is open, expand Security Settings and then click on the Software Restriction Policies section. If you do not see the items in the right pane as shown above, you will need to add a new policy. To do this click on the Action button and select New Software Restriction Policies. This will then enable the policy and the right pane will appear as in the image above. You should then click on the Additional Rules category and then right-click in the right pane and select New Path Rule.... You should then add a Path Rule for each of the items listed below.If the Software Restriction Policies cause issues when trying to run legitimate applications, you should see this section on how to enable specific applications.Below are a few Path Rules that are suggested you use to not only block the infections from running, but also to block attachments from being executed when opened in an e-mail client.Block TeslaCrypt executable in %AppData%Path: %AppData%\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from %AppData%.Block TeslaCrypt executable in %LocalAppData%Path if using Windows XP: %UserProfile%\Local Settings\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from %AppData%.Block Zbot executable in %AppData%Path: %AppData%\*\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from immediate subfolders of %AppData%.Block Zbot executable in %LocalAppData%Path if using Windows XP: %UserProfile%\Local Settings\*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\*\*.exe
Security Level: Disallowed
Description: Don't allow executables to run from immediate subfolders of %AppData%.Block executables run from archive attachments opened with WinRAR:Path if using Windows XP: %UserProfile%\Local Settings\Temp\Rar*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\Rar*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with WinRAR.Block executables run from archive attachments opened with 7zip:Path if using Windows XP: %UserProfile%\Local Settings\Temp\7z*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\7z*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with 7zip.Block executables run from archive attachments opened with WinZip:Path if using Windows XP: %UserProfile%\Local Settings\Temp\wz*\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\wz*\*.exe
Security Level: Disallowed
Description: Block executables run from archive attachments opened with WinZip.Block executables run from archive attachments opened using Windows built-in Zip support:Path if using Windows XP: %UserProfile%\Local Settings\Temp\*.zip\*.exe
Path if using Windows Vista/7/8: %LocalAppData%\Temp\*.zip\*.exe
Security Level: Disallowed
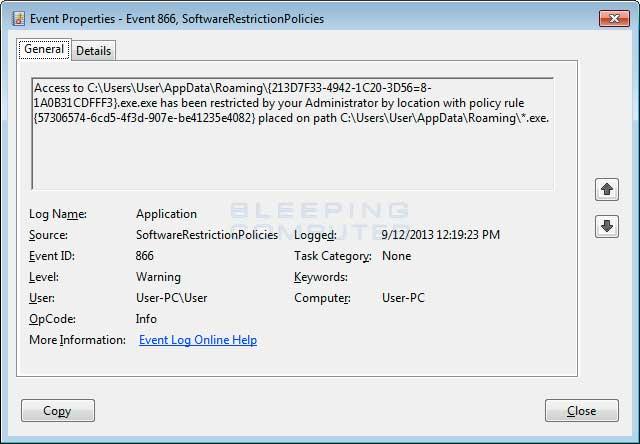
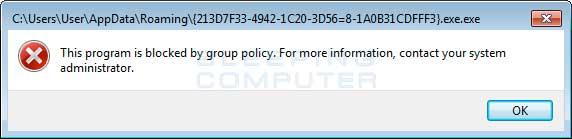
Description: Block executables run from archive attachments opened using Windows built-in Zip support.You can see an event log entry and alert showing an executable being blocked:If you need help configuring this, feel free to ask in the TeslaCrypt help topic or Alpha Crypt help topic.How to allow specific applications to run when using Software Restriction Policies
If you use Software Restriction Policies, or CryptoPrevent, to block TeslaCrypt you may find that some legitimate applications no longer run. This is because some companies mistakenly install their applications under a user's profile rather than in the Program Files folder where they belong. Due to this, the Software Restriction Policies will prevent those applications from running.Thankfully, when Microsoft designed Software Restriction Policies they made it so a Path Rule that specifies a program is allowed to run overrides any path rules that may block it. Therefore, if a Software Restriction Policy is blocking a legitimate program, you will need to use the manual steps given above to add a Path Rule that allows the program to run. To do this you will need to create a Path Rule for a particular program's executable and set the Security Level to Unrestricted instead of Disallowed as shown in the image below.Once you add these Unrestricted Path Rules, the specified applications will be allowed to run again.TeslaCrypt Timeline
- TeslaCrypt Timeline
+ إنشاء موضوع جديد
النتائج 1 إلى 1 من 1
-
25-10-2015, 01:07 #1
 TeslaCrypt and Alpha Crypt Ransomware Information Guide and FAQ
TeslaCrypt and Alpha Crypt Ransomware Information Guide and FAQ
المواضيع المتشابهه
-
TeslaCrypt Ransomware. Virus .exx, .xyz, .zzz, .aaa, .abc or .ccc
بواسطة Eng Amr Adel في المنتدى قسم الانتى فيروس Virusesمشاركات: 1آخر مشاركة: 17-01-2016, 15:40 -
Remove File Recovery virus (Uninstall Guide)
بواسطة Eng Amr Adel في المنتدى قسم الانتى فيروس Virusesمشاركات: 0آخر مشاركة: 25-10-2015, 00:41 -
.ccc Extension / howto_recover_file Ransomware Removal Guide
بواسطة Eng Amr Adel في المنتدى قسم الانتى فيروس Virusesمشاركات: 0آخر مشاركة: 25-10-2015, 00:06 -
Guide to Edit Your name.com SPF Record
بواسطة Rise Company في المنتدى قسم الايميلات Emailsمشاركات: 0آخر مشاركة: 12-05-2014, 14:22 -
كتاب : The Oxford Guide to English Usage
بواسطة Eng Amr Adel في المنتدى رايز للمواضيع العام Rise Generalمشاركات: 0آخر مشاركة: 07-12-2009, 15:50







 رد مع اقتباس
رد مع اقتباس
المفضلات