الحماية Whitelist والحظر Blocking سياسة أمان المحتوى CSP Content Security Policy - الكوردوفا و الفون جاب
الكوردوفا و الفون جاب Phone Gap / Cordova
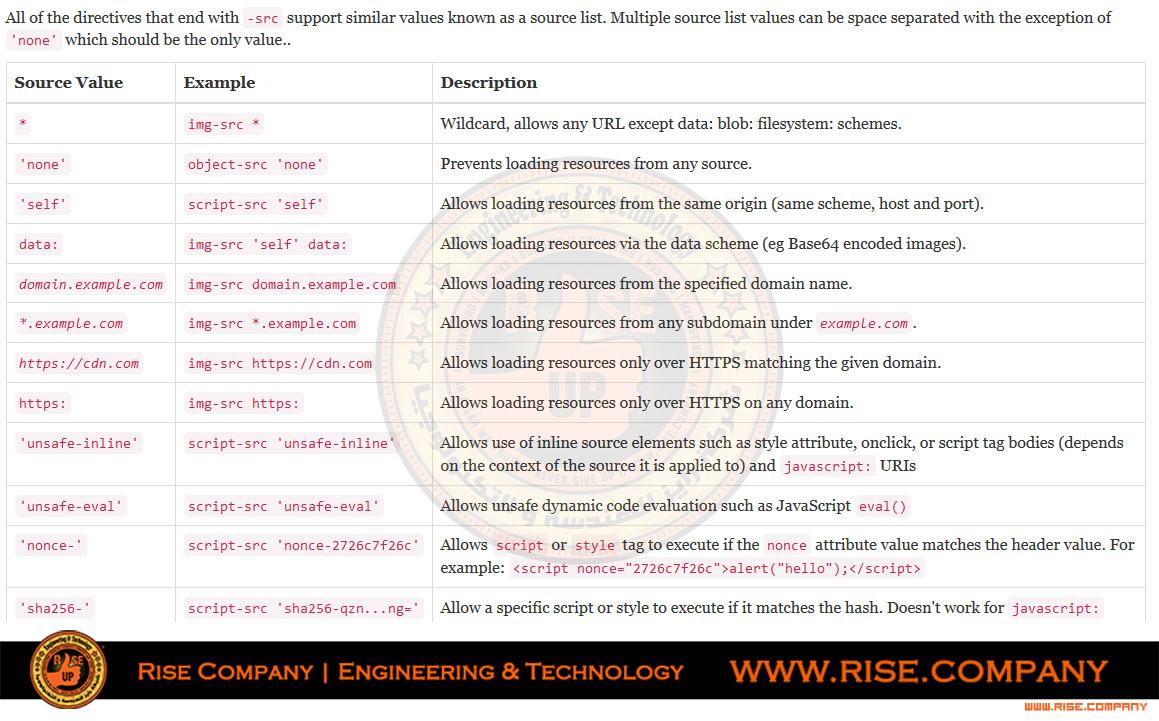
شرح الميتا CSP المسئولة عن الحماية / السكيورتي / الصلاحيات / الحظر لوظائف التطبيق
قد تجد انك قمت بتنزيل بلوجن plugin وعند وضع فنكشن function لا تجده يعمل !!!
جميع وظائف api للجافا سكربت داخل index.html او داخل index.js
محظوره و السبب هو كود ميتا Meta
الوصف :كود:<meta http-equiv="Content-Security-Policy" content="default-src 'self' data: gap: https://ssl.gstatic.com 'unsafe-eval'; style-src 'self' 'unsafe-inline'; media-src *; img-src 'self' data: content:;">
يوضح هنا ان هناك 3 اشياء تفعلها هذه الميتا ,
الاول هو مخاطبة الجافا سكربت مع لغة الاندرويد النيتف
الثانى هو مخاطبة سكربت مع لغة الاى فون النيتف
الثالث هو تعطيل استخدام البلوجن من أجل الحماية
الكود المسئول عن حظر البلوجن / السكربت :كود:<!-- Customize this policy to fit your own app's needs. For more guidance, see: https://github.com/apache/cordova-plugin-whitelist/blob/master/README.md#content-security-policy Some notes: * gap: is required only on iOS (when using UIWebView) and is needed for JS->native communication * https://ssl.gstatic.com is required only on Android and is needed for TalkBack to function properly * Disables use of inline scripts in order to mitigate risk of XSS vulnerabilities. To change this: * Enable inline JS: add 'unsafe-inline' to default-src -->
كود:<meta http-equiv="Content-Security-Policy" content="default-src 'self' data: gap: https://ssl.gstatic.com 'unsafe-eval'; style-src 'self' 'unsafe-inline'; media-src *; img-src 'self' data: content:;">
ما هو self ؟
هو السماح بتحميل res من المخطط الاصلى فقط
ما هو unsafe-inline ؟
هو السماح بتحميل res من اى مكان
ما هو unsafe-eval ؟
هو السماح للجافا سكربت بمخاطبة الاندرويد النيتف
ما هو gap ؟
هو السماح للجافا سكربت بمخاطبة الاى فون النيتف
ما هو https://ssl.gstatic.com ؟
هو مهام TalkBack (accessibility) الموجودة فى الاندرويد النيتف
الكود المعدل المناسب لكك للعمل بدون قيود :
هو ان تضيف للكود الاساسى لك
ليكون كالتالىكود:script-src * 'unsafe-inline';
كما يمكنك حذف السطر نهائيا فسيعمل التطبيق بشكل ممتاز دون مشاكلكود:<meta http-equiv="Content-Security-Policy" content=" default-src *; style-src * 'unsafe-inline'; script-src * 'unsafe-inline'; media-src *; img-src * data:; " />
ولكن لا نعلم ان كان سيتوقف عند النشر على المتجر ام لا.
المرجع :This policy allows images, scripts, AJAX, and CSS from the same origin, and does not allow any other resources to load (eg object, frame, media, etc).
https://content-security-policy.com/
جميع الاكواد فى المرفقات
+ إنشاء موضوع جديد
النتائج 1 إلى 1 من 1
-
25-07-2017, 22:30 #1Status
- Offline





- تاريخ التسجيل
- Apr 2014
- الدولة
- Egypt
- المشاركات
- 4,642
 Engineering and Technology
Engineering and Technology
- معدل تقييم المستوى
- 10
 الحماية والحظر سياسة أمان المحتوى CSP Content Security Policy - الكوردوفا و الفون جاب
------------------------------------------------------------------------
الحماية والحظر سياسة أمان المحتوى CSP Content Security Policy - الكوردوفا و الفون جاب
------------------------------------------------------------------------
شركة رايز للهندسة و التكنولوجيا Rise Company for Engineering & Technology
------------------------------------------------------------------------
Web Hosting | Web Designing | E-Marketing
رقم # 1 فى خدمات الشركات Business Services
استضافة مواقع Web Hosting - عمل ايميل شركة Business Emails
تصميم موقع شركة Web Design - تسويق الكترونى على جوجل Google Adwords
www.rise.company | www.rise.company/emails
ملحوظة : جميع خدماتنا مخصصة للشركات فقط وغير متاحة للافراد
وليس لنا اى منتجات او صيانة نهائيا! يرجى الانتباه الى ذلك.
المواضيع المتشابهه
-
معلومات و نصائح لمطورى الفون جاب و الكوردوفا Cordova/Phonegap
بواسطة Rise Company في المنتدى قسم الكوردوفا Ionic/Cordovaمشاركات: 0آخر مشاركة: 16-07-2017, 01:06 -
دورة كاملة عن الكوردوفا و الفون جاب Phone Gap / Cordova من 60 حلقة
بواسطة Rise Company في المنتدى قسم الكوردوفا Ionic/Cordovaمشاركات: 0آخر مشاركة: 27-06-2017, 23:00 -
شرح wp security الحماية الشاملة للووردبريس All in one WP security
بواسطة Rise Company في المنتدى قسم ووردبريس WordPressمشاركات: 0آخر مشاركة: 12-06-2017, 18:53 -
حصريا برنامج الحماية الرائع ESET Smart Security 4.2.22.0 Beta للحماية الشاملة
بواسطة Eng Amr Adel في المنتدى رايز للكمبيوتر Rise Computerمشاركات: 0آخر مشاركة: 22-12-2009, 22:35 -
برنامج الحماية الرائع ESET Smart Security 4.2.22.0 Beta
بواسطة Eng Amr Adel في المنتدى رايز للكمبيوتر Rise Computerمشاركات: 0آخر مشاركة: 22-12-2009, 21:35



 رد مع اقتباس
رد مع اقتباس
المفضلات