فايروول السي بانل Whm / Cpanel CSF Firewall تفعيل WARNING: RESTRICT_SYSLOG is disable
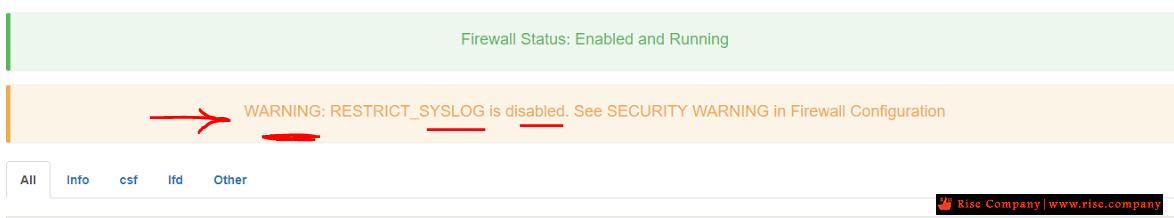
WARNING: RESTRICT_SYSLOG is disabled. See SECURITY WARNING in Firewall Configuration
حل مشكله رسالة RESTRICT_SYSLOG is disabled بعد تثبيت CSF
RESTRICT_SYSLOG warning in csf cpanel plugin
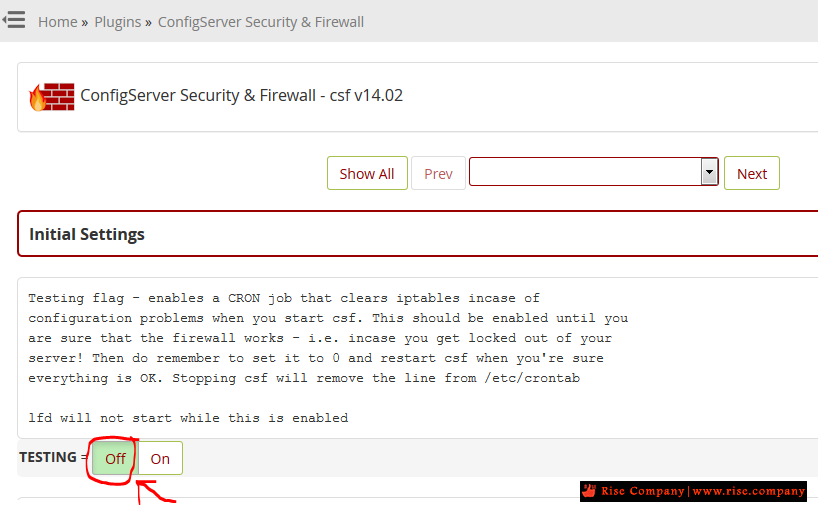
بعد تثبيت الفايروول CSF يتطلب بعد تثبيته عمل شيئين مهمين
الاول هو جعل TESTING =OFF حتى ينشط عمل Firewall
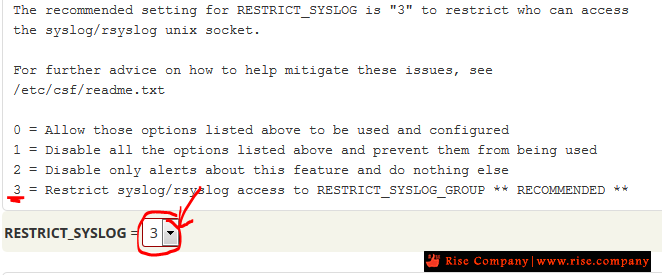
ثم يتم جعل القيمة امامها RESTRICT_SYSLOG = 3 بدل من 0
RESTRICT_SYSLOG = "0" and changing it to RESTRICT_SYSLOG = "3"
وهى المسئولة عن حماية ضمن الهجمات brute force attacks
SECURITY WARNING
================
Unfortunately, syslog and rsyslog allow end-users to log messages to some
system logs via the same unix socket that other local services use. This
means that any log line shown in these system logs that syslog or rsyslog
maintain can be spoofed (they are exactly the same as real log lines).
Since some of the features of lfd rely on such log lines, spoofed messages
can cause false-positive matches which can lead to confusion at best, or
blocking of any innocent IP address or making the server inaccessible at
worst.
Any option that relies on the log entries in the files listed in
/etc/syslog.conf and /etc/rsyslog.conf should therefore be considered
vulnerable to exploitation by end-users and scripts run by end-users.
NOTE: Not all log files are affected as they may not use syslog/rsyslog
The option RESTRICT_SYSLOG disables all these features that rely on affected
logs. These options are:
LF_SSHD LF_FTPD LF_IMAPD LF_POP3D LF_BIND LF_SUHOSIN LF_SSH_EMAIL_ALERT
LF_SU_EMAIL_ALERT LF_CONSOLE_EMAIL_ALERT LF_DISTATTACK LF_DISTFTP
LT_POP3D LT_IMAPD PS_INTERVAL UID_INTERVAL WEBMIN_LOG LF_WEBMIN_EMAIL_ALERT
PORTKNOCKING_ALERT LF_SUDO_EMAIL_ALERT
This list of options use the logs but are not disabled by RESTRICT_SYSLOG:
ST_ENABLE SYSLOG_CHECK LOGSCANNER CUSTOM*_LOG
The following options are still enabled by default on new installations so
that, on balance, csf/lfd still provides expected levels of security:
LF_SSHD LF_FTPD LF_POP3D LF_IMAPD LF_SSH_EMAIL_ALERT LF_SU_EMAIL_ALERT
If you set RESTRICT_SYSLOG to "0" or "2" and enable any of the options listed
above, it should be done with the knowledge that any of the those options
that are enabled could be triggered by spoofed log lines and lead to the
server being inaccessible in the worst case. If you do not want to take that
risk you should set RESTRICT_SYSLOG to "1" and those features will not work
but you will not be protected from the exploits that they normally help block
The recommended setting for RESTRICT_SYSLOG is "3" to restrict who can access
the syslog/rsyslog unix socket.
For further advice on how to help mitigate these issues, see
/etc/csf/readme.txt
0 = Allow those options listed above to be used and configured
1 = Disable all the options listed above and prevent them from being used
2 = Disable only alerts about this feature and do nothing else
3 = Restrict syslog/rsyslog access to RESTRICT_SYSLOG_GROUP ** RECOMMENDED **The following setting is used if RESTRICT_SYSLOG is set to 3. It restricts
write access to the syslog/rsyslog unix socket(s). The group must not already
exists in /etc/group before setting RESTRICT_SYSLOG to 3, so set the option
to a unique name for the server
You can add users to this group by changing /etc/csf/csf.syslogusers and then
restarting lfd afterwards. This will create the system group and add the
users from csf.syslogusers if they exist to that group and will change the
permissions on the syslog/rsyslog unix socket(s). The socket(s) will be
monitored and the permissions re-applied should syslog/rsyslog be restarted
Using this option will prevent some legitimate logging, e.g. end-user cron
job logs
If you want to revert RESTRICT_SYSLOG to another option and disable this
feature, change the setting of RESTRICT_SYSLOG and then restart lfd and then
syslog/rsyslog and the unix sockets will be reset
+ إنشاء موضوع جديد
النتائج 1 إلى 1 من 1
-
04-04-2020, 19:08 #1Status
- Offline





- تاريخ التسجيل
- Apr 2014
- الدولة
- Egypt
- المشاركات
- 4,619
 Engineering and Technology
Engineering and Technology
- معدل تقييم المستوى
- 10
 فايروول السي بانل Whm / Cpanel CSF Firewall تفعيل WARNING: RESTRICT_SYSLOG is disable
------------------------------------------------------------------------
فايروول السي بانل Whm / Cpanel CSF Firewall تفعيل WARNING: RESTRICT_SYSLOG is disable
------------------------------------------------------------------------
شركة رايز للهندسة و التكنولوجيا Rise Company for Engineering & Technology
------------------------------------------------------------------------
Web Hosting | Web Designing | E-Marketing
رقم # 1 فى خدمات الشركات Business Services
استضافة مواقع Web Hosting - عمل ايميل شركة Business Emails
تصميم موقع شركة Web Design - تسويق الكترونى على جوجل Google Adwords
www.rise.company | www.rise.company/emails
ملحوظة : جميع خدماتنا مخصصة للشركات فقط وغير متاحة للافراد
وليس لنا اى منتجات او صيانة نهائيا! يرجى الانتباه الى ذلك.
المواضيع المتشابهه
-
فايروول السي بانل Whm / Cpanel APF Firewall شرح Advanced Policy Firewall
بواسطة Rise Company في المنتدى قسم حماية Whm / Cpanelمشاركات: 0آخر مشاركة: 31-03-2020, 23:12 -
فهرس : كل شىء عن فايروول السي بانل Whm / Cpanel CSF Firewall
بواسطة Rise Company في المنتدى قسم فايروول CSFمشاركات: 0آخر مشاركة: 19-08-2019, 00:27 -
فايروول السي بانل Whm / Cpanel CSF Firewall شرح الحذف Uninstall
بواسطة Rise Company في المنتدى قسم فايروول CSFمشاركات: 0آخر مشاركة: 25-12-2018, 06:55 -
فايروول السي بانل Whm / Cpanel CSF Firewall شرح فتح FTP
بواسطة Rise Company في المنتدى قسم فايروول CSFمشاركات: 0آخر مشاركة: 13-06-2018, 12:04 -
فايروول السي بانل Whm / Cpanel CSF Firewall شرح التثبيت
بواسطة Rise Company في المنتدى قسم فايروول CSFمشاركات: 0آخر مشاركة: 02-06-2018, 15:16



 رد مع اقتباس
رد مع اقتباس
المفضلات